Cyber Security – Complete Notes for IBPS, SSC, RRB & Govt Exams
Cyber Security is one of the most important and consistently tested chapters in IBPS, SSC CGL, RRB NTPC, LIC AAO, and all government job exams — especially in banking where digital security is a daily operational concern. This post covers everything — components of security, cryptography, all types of malware (viruses, worms, trojans, ransomware, spyware), all types of cyber attacks, complete security solutions (firewall, antivirus, VPN, MFA, encryption, digital signature, biometrics), file access permissions, and Indian cyber laws (IT Act 2000, DPDP Act 2023) — with memory tricks, one-liners, and 10 exam-focused FAQs.
Jump to section
- Introduction: Why Cyber Security is Critical for Banking Exams
- What is Cyber Security?
- Components (Goals) of Security
- Cryptography - The Science of Secure Communication
- Types of Malware - Complete Guide
- Types of Cyber Attacks
- Security Solutions - Complete Guide
- File Access Permissions
- Other Security Terms
- Cyber Laws in India
- Memory Tricks
- One-Liner Recap (Quick Revision)
Introduction: Why Cyber Security is Critical for Banking Exams
India's banking sector processes over 9.41 billion UPI transactions per month (2024). Every one of these transactions is a potential target for cybercriminals. Banks are the most targeted sector for cyber attacks — making Cyber Security knowledge essential not just for passing the exam, but for performing effectively on the job.
In government job exams, Cyber Security is tested across multiple difficulty levels:
- "VIRUS stands for ___?" → Vital Information Resources Under Siege
- "Which malware encrypts your files and demands ransom?" → Ransomware
- "The first computer virus was ___?" → Creeper (1971)
- "WannaCry is an example of ___?" → Ransomware
- "Which attack floods a server with requests?" → DDoS (Distributed Denial of Service)
- "IT Act was enacted in which year?" → 2000
- "CERT-In stands for ___?" → Computer Emergency Response Team India
This chapter is also where banking awareness meets computer awareness — phishing attacks on banking customers, ATM skimming, UPI fraud, and data breach notifications are everyday banking news items. Mastering Cyber Security makes you a better-prepared exam candidate AND a more effective banking professional.
What is Cyber Security?
Cyber Security (also called Computer Security or IT Security) is the practice of protecting computer systems, networks, programs, and data from unauthorised access, damage, attack, or theft.
Scope of Cyber Security:
- Protecting hardware (servers, computers, mobile devices) from physical tampering
- Protecting software (operating systems, applications) from malware and exploits
- Protecting data (stored data, data in transit) from theft and corruption
- Protecting networks from intrusion and interception
- Protecting users from social engineering and fraud
Why Cyber Security matters in banking:
- Customer financial data is extremely sensitive
- A single data breach can expose millions of accounts
- Regulatory requirements (RBI, SEBI, IRDAI) mandate strong security
- Trust is the foundation of banking — one attack can destroy years of reputation
Components (Goals) of Security
Security is not just about preventing unauthorised access — it has multiple dimensions:
| Component | Description | Example |
|---|---|---|
| Confidentiality | Ensuring data is accessible only to authorised persons — preventing unauthorised disclosure | Bank account details visible only to the account holder and authorised staff |
| Integrity | Ensuring data is not altered without detection — preventing unauthorised modification | Ensuring a ₹1,000 transaction doesn't become ₹10,000 through tampering |
| Authentication | Verifying that users are who they claim to be | Login with password, OTP, or biometric |
| Access Control | Ensuring users can only access the resources they are authorised to use | A bank clerk can view accounts but cannot approve loans |
| Non-Repudiation | Ensuring the sender cannot deny having sent a message or transaction | Digital signatures on electronic contracts |
| Availability | Ensuring systems are operational and accessible when needed | Bank's internet banking available 24×7 |
| Privacy | Individual rights over their own personal information | Right to know what data a bank holds about you |
| Steganography | The art of hiding the existence of a message within another medium | Hiding a secret message inside an image file |
Cryptography - The Science of Secure Communication
Cryptography is the science of writing and reading messages in secret form — converting data into an unreadable format that can only be decoded by authorised parties.
Steganography vs Cryptography:
- Steganography — hides the existence of a message (the message is there, you just can't see it)
- Cryptography — hides the content of a message (the message is visible, but unreadable)
Key Cryptography Terms
| Term | Definition |
|---|---|
| Plain Text | The original, readable message before encryption |
| Cipher Text | The encrypted, scrambled, unreadable message after encryption |
| Encryption | The process of converting plain text → cipher text using a mathematical algorithm and key |
| Decryption | The process of converting cipher text → plain text (reversing encryption) |
| Cipher | The mathematical algorithm used for encryption and decryption |
| Key | A piece of data used by the cipher to encrypt/decrypt — like a password for the cipher |
| Cryptanalysis | The science of breaking encryption without the key — "code-breaking" |
Types of Encryption
| Type | How It Works | Key Used | Speed | Example |
|---|---|---|---|---|
| Symmetric Encryption | Same key used for both encryption and decryption | One shared key | Faster | AES (Advanced Encryption Standard), DES, 3DES |
| Asymmetric Encryption | Different keys — a Public Key (shared with everyone, used to encrypt) and a Private Key (kept secret, used to decrypt) | Key pair | Slower | RSA, ECC — used in HTTPS, digital signatures |
How HTTPS Works (Asymmetric + Symmetric):
- Website sends its Public Key (in SSL certificate) to your browser
- Browser encrypts a random session key using the website's Public Key
- Website decrypts it using its Private Key
- Both now share a secret session key
- All further communication uses Symmetric Encryption (faster) with that session key
Types of Malware - Complete Guide
Malware (Malicious Software) is any software intentionally designed to disrupt, damage, or gain unauthorised access to a computer system.
Computer Virus
VIRUS = Vital Information Resources Under Siege
A computer virus is a self-replicating malicious program that attaches itself to legitimate files or programs and spreads when infected files are executed.
Key Virus Facts:
- First computer virus: Creeper (1971) — displayed "I'm the Creeper, catch me if you can!" and replicated across ARPANET
- First PC boot sector virus: Brain (1986) — created in Pakistan by the Alvi brothers
- Viruses require human action to spread (running an infected file, opening an attachment)
- They attach to host files — unlike worms which are standalone
Types of Viruses
| Virus Type | How It Works | Example |
|---|---|---|
| Resident Virus | Lodges itself permanently in RAM; infects every file opened during the session | Randex, CMJ |
| Direct Action Virus | Activates only when the infected file is executed; otherwise dormant | Vienna virus |
| Overwrite Virus | Deletes and replaces the original file content with malicious code — original file destroyed | Way, Trj.Reboot |
| Boot Sector Virus | Infects the Master Boot Record (MBR) of the hard disk; executes every time the computer starts | Polyboot.B, AntiEXE |
| Macro Virus | Infects macro-enabled documents (.doc, .xls, .ppt); spreads via email attachments | Melissa.A (1999), Concept |
| Polymorphic Virus | Changes its own code with each infection to avoid signature-based antivirus detection | Elkern, Marburg |
| Multipartite Virus | Spreads through multiple methods (boot sector + file infection) simultaneously | Flip, Invader |
| FAT Virus | Attacks the File Allocation Table — corrupts pointers to file locations | — |
| Web Scripting Virus | Embedded in malicious website code; executes when the page is visited | JS.Fortnight |
| Ransomware | Encrypts victim's files and demands ransom payment (usually cryptocurrency) for the decryption key | WannaCry, LockBit, Petya |
Worm
| Feature | Details |
|---|---|
| Definition | Self-replicating malicious program that spreads across networks without requiring human action and without attaching to a host file |
| Key difference from virus | Virus needs human action (opening a file) + attaches to files; Worm spreads automatically + is standalone |
| How it spreads | Exploits network vulnerabilities, email, shared drives — automatically scans for vulnerable systems |
| Damage | Consumes network bandwidth; can install backdoors; may carry additional payloads |
| Examples | Morris Worm (1988 — first famous worm), Nimda, Blaster, Sasser, ILOVEYOU |
| Visibility | Creates invisible files — hard to detect |
Trojan Horse
| Feature | Details |
|---|---|
| Definition | Malware disguised as legitimate, useful software — tricks users into installing it |
| Key difference | Does NOT self-replicate — must be installed by the user (unlike virus and worm) |
| What it does | Once installed: creates backdoors, steals data, downloads more malware, gives attacker remote access |
| Named after | The Trojan Horse from Greek mythology — appears friendly, is actually an attack |
| Examples | Zeus (banking trojan — stole banking credentials), Emotet, RAT (Remote Access Trojan) |
Spyware
| Feature | Details |
|---|---|
| Definition | Software that secretly monitors user activity and collects personal information without consent |
| What it collects | Keystrokes, browsing history, passwords, banking credentials, screenshots, webcam feeds |
| How it spreads | Bundled with free software, malicious websites, email attachments |
| Examples | FinFisher (government-grade spyware), Keyloggers, CoolWebSearch |
Adware
| Feature | Details |
|---|---|
| Definition | Software that automatically displays or downloads advertisements — often without user consent |
| Harm level | Generally less harmful than other malware but very annoying; may slow system; can redirect browsers |
| Revenue model | Attacker earns money every time an ad is displayed or clicked |
| Examples | Many "free" mobile apps include adware; browser hijackers |
Ransomware
| Feature | Details |
|---|---|
| Definition | Malware that encrypts the victim's files and demands a ransom payment (usually in cryptocurrency — Bitcoin) to provide the decryption key |
| Severity | Extremely damaging — organisations have lost billions of dollars |
| Notable attacks | WannaCry (2017) — infected 200,000+ computers in 150 countries in 3 days; targeted hospitals, telecoms, banks |
| Other examples | Petya/NotPetya, LockBit, REvil, DarkSide (Colonial Pipeline attack) |
| Prevention | Regular backups; up-to-date patches; email security; network segmentation |
Rootkit
| Feature | Details |
|---|---|
| Definition | Malware that gains administrative (root) access to a system and hides itself from the OS and antivirus tools |
| Why dangerous | Extremely difficult to detect — it modifies the OS itself to hide its presence; gives attacker persistent, hidden control |
| Removal | Often requires complete OS reinstallation |
| Examples | Sony BMG rootkit, Necurs, Azazel |
Logic Bomb
| Feature | Details |
|---|---|
| Definition | Malicious code embedded in legitimate software that activates when specific conditions are met (date, time, event, user action) |
| Also called | Slag code, time bomb (when triggered by date/time) |
| Example | Code that deletes all financial records on January 1st; code triggered when a specific employee's ID is removed from the system (planted by a disgruntled employee) |
| Detection | Very hard to detect before it activates |
Keylogger
| Feature | Details |
|---|---|
| Definition | Software (or hardware) that records every keystroke typed on the computer — capturing passwords, credit card numbers, messages |
| Type | Can be software-based or hardware-based (physical device inserted between keyboard and computer) |
| Use | Often installed by spyware/trojans; used in ATM skimming |
| Legitimate use | Parental controls, employee monitoring (with consent) |
Malware Types - Quick Comparison Table
| Malware | Replicates? | Needs Host File? | Spreads Automatically? | Primary Damage |
|---|---|---|---|---|
| Virus | Yes | Yes (attaches) | No (needs human action) | File corruption, data theft |
| Worm | Yes | No (standalone) | Yes (network) | Bandwidth consumption, backdoors |
| Trojan | No | No (disguised app) | No | Backdoor, data theft |
| Ransomware | Varies | No | Varies | File encryption, extortion |
| Spyware | No | No | No | Surveillance, data theft |
| Adware | No | No | No | Unwanted ads |
| Rootkit | No | No | No | Hidden admin access |
| Logic Bomb | No | Yes (embedded) | No | Timed/conditional damage |
| Keylogger | No | No | No | Credential theft |
Types of Cyber Attacks
| Attack | Description | Example |
|---|---|---|
| Hacking | Unauthorised access to computer systems or networks — exploiting vulnerabilities | Breaking into a bank's server |
| Cracking | Breaking into computers to steal data; using password crackers or exploits | Brute-forcing a password |
| Phishing | Fraudulently obtaining sensitive information (passwords, card numbers) by impersonating a trusted entity via fake emails/websites | Fake SBI email asking you to update your net banking password |
| Vishing | Voice phishing — fraud via phone calls impersonating banks/government | "I'm calling from SBI — please share your OTP" |
| Smishing | SMS phishing — fraud via text messages with malicious links | Fake message: "Your account blocked — click here" |
| Spoofing / Masquerade | Impersonating another user, system, or IP address to gain trust | IP Spoofing — faking source IP; Email spoofing |
| Salami Technique | Diverting tiny amounts from many accounts (e.g., ₹0.50 per transaction) — individually unnoticeable but collectively significant | Fraudulent rounding of interest calculations |
| Spam | Unsolicited bulk emails — commercial, fraudulent, or malicious | Flood of promotional/scam emails |
| DDoS (Distributed Denial of Service) | Flooding a server/website with millions of fake requests from many compromised computers, making it unavailable to legitimate users | Attacking IRCTC during Tatkal booking |
| DoS (Denial of Service) | Same as DDoS but from a single source — server overwhelmed by requests | — |
| Man-in-the-Middle (MitM) | Attacker secretly intercepts and potentially alters communication between two parties who believe they're communicating directly | Intercepting unencrypted banking traffic on public Wi-Fi |
| Zero-Day Attack | Exploiting a newly discovered, unpatched vulnerability — the vendor has zero days to fix it before it's exploited | Exploiting a browser bug before the vendor releases a patch |
| Supply Chain Attack | Attacking software through a trusted third-party vendor — compromising the software supply chain | SolarWinds attack (2020) — malware inserted into software updates |
| Social Engineering | Manipulating people psychologically into revealing confidential information or performing security-compromising actions | Attacker calls IT desk pretending to be a senior manager, requests password reset |
| SQL Injection | Inserting malicious SQL code into a web form to manipulate the database | Entering ' OR '1'='1 in a login form to bypass authentication |
| Cross-Site Scripting (XSS) | Injecting malicious scripts into web pages viewed by other users | Stealing session cookies of logged-in users |
| Deepfake | AI-generated fake video or audio used for fraud or disinformation | Fake CEO video authorising fraudulent bank transfer |
| Cryptojacking | Secretly using a victim's computer to mine cryptocurrency without their knowledge | Hidden scripts on websites using your CPU to mine Bitcoin |
| Ransomware Attack | WannaCry (2017) — affected 200,000+ computers in 150 countries | Encrypted NHS hospital records in UK |
Security Solutions - Complete Guide
Antivirus Software
| Feature | Details |
|---|---|
| Purpose | Detects, quarantines, and removes malware (viruses, worms, trojans, spyware) |
| How it works | Signature-based detection (known malware patterns), heuristic analysis (suspicious behaviour), sandboxing |
| Popular products | Kaspersky, Norton, Quick Heal (India), McAfee, Avast, Windows Defender (built-in), Bitdefender |
| Limitation | Signature-based detection cannot catch zero-day malware (new, unknown threats) |
Firewall
| Feature | Details |
|---|---|
| Purpose | Monitors and filters incoming and outgoing network traffic based on predefined security rules |
| How it works | Acts as a barrier between trusted internal network and untrusted external network (internet); blocks unauthorised traffic |
| Types | Software firewall (installed on a computer — Windows Firewall); Hardware firewall (physical device protecting entire network) |
| Cannot stop | Threats that come from inside the network; social engineering attacks |
Password Security
| Aspect | Guidelines |
|---|---|
| Strong password | Mix of uppercase + lowercase letters + numbers + special symbols (@#$%); minimum 12 characters |
| Weak password | Names, dates of birth, common words, simple sequences (123456, password) |
| Good practices | Use different passwords for different accounts; change regularly; use password manager |
| Two-Factor | Always enable 2FA/MFA for sensitive accounts |
Digital Certificate
| Feature | Details |
|---|---|
| Definition | An electronic document that verifies the identity of an entity (person, server, organisation) and contains their public key |
| Issued by | CA (Certificate Authority) — trusted third parties (DigiCert, VeriSign, Let's Encrypt) |
| Used in | HTTPS (the padlock in your browser); code signing; email authentication |
| Contains | Owner's name, public key, expiry date, CA signature |
| Example | When you visit https://www.sbi.co.in, your browser verifies SBI's digital certificate before establishing a secure connection |
Digital Signature
| Feature | Details |
|---|---|
| Definition | An electronic equivalent of a handwritten signature — authenticates the sender and ensures the content has not been altered |
| How it works | Sender creates a hash of the message → encrypts the hash with their Private Key → attaches to message; Receiver decrypts with sender's Public Key → verifies hash matches |
| Properties | Authentication (proves sender identity), Integrity (detects tampering), Non-repudiation (sender cannot deny sending) |
| Legal status | Legally valid in India under the IT Act 2000 |
| Used in | E-filing of income tax, MCA filings, legal contracts, banking authorisations |
VPN (Virtual Private Network)
| Feature | Details |
|---|---|
| Definition | Creates an encrypted tunnel between your device and a VPN server — all traffic passes through this tunnel, hidden from ISPs, hackers, and surveillance |
| Benefits | Encrypts internet traffic; hides real IP address; bypasses geo-restrictions; secure public Wi-Fi usage |
| Used by | Remote workers accessing corporate networks; privacy-conscious users; journalists in restricted countries |
| Examples | NordVPN, ExpressVPN, Cisco AnyConnect (enterprise) |
MFA / 2FA (Multi-Factor Authentication)
| Feature | Details |
|---|---|
| Definition | Requires users to prove identity using two or more different factors before access is granted |
| Three authentication factors | Something you know (password, PIN); Something you have (OTP, hardware token, mobile phone); Something you are (fingerprint, face recognition, iris scan) |
| Why it matters | Even if your password is stolen, an attacker cannot access your account without the second factor |
| Examples | Net banking (password + OTP); Google (password + authenticator app); ATM (card + PIN) |
Biometric Authentication
| Feature | Details |
|---|---|
| Definition | Authentication using unique biological characteristics |
| Types | Fingerprint, Face recognition (Apple Face ID, Windows Hello), Iris scan, Voice recognition, Palm vein scan |
| Advantages | Cannot be forgotten; cannot be easily stolen/replicated; convenient |
| Used in | Smartphone unlock, Aadhaar authentication (UIDAI), airport immigration, banking KYC |
CAPTCHA
| Feature | Details |
|---|---|
| Full Form | Completely Automated Public Turing test to tell Computers and Humans Apart |
| Purpose | Distinguishes human users from automated bots |
| How it works | Presents a challenge that is easy for humans but hard for computers (distorted text, image recognition, click challenges) |
| Types | Text-based, image-based, reCAPTCHA (Google), invisible CAPTCHA (background analysis) |
| Used in | Website registrations, form submissions, preventing automated attacks |
End-to-End Encryption (E2EE)
| Feature | Details |
|---|---|
| Definition | Data is encrypted on the sender's device and can only be decrypted by the intended recipient's device — no one in between (including the service provider) can read it |
| Examples | WhatsApp, Signal, iMessage — even WhatsApp servers cannot read your messages |
| Importance | Maximum privacy; government/ISP cannot intercept content |
Zero Trust Security
| Feature | Details |
|---|---|
| Principle | "Never trust, always verify" — no user, device, or system is automatically trusted, even inside the corporate network |
| Traditional model | "Trust but verify" — users inside the network perimeter are trusted by default |
| Zero Trust model | Every access request must be authenticated, authorised, and continuously validated regardless of location |
| Why needed | Cloud computing, remote work, and mobile devices have dissolved the traditional network perimeter |
File Access Permissions
In operating systems, files and folders have three basic permission types that control what users can do with them:
| Permission | What It Allows |
|---|---|
| Read (r) | Can view/open the file content; cannot modify |
| Write (w) | Can modify or delete the file content |
| Execute (x) | Can run the file as a program/script |
Permissions can be set for three categories of users:
- Owner — the user who created the file
- Group — users belonging to the file's group
- Others — all other users
Other Security Terms
| Term | Meaning |
|---|---|
| Eavesdropping | Monitoring/intercepting network transmissions to capture content — passive attack |
| Proxy Server | An intermediary server that hides the client's real network address; can filter content and improve security |
| Application Gateway | A firewall that applies security policies to specific applications (FTP, HTTP, Telnet) at the application layer |
| Ethical Hacking | Authorised penetration testing to find and fix vulnerabilities — attackers are paid to find weaknesses before real attackers do |
| CEH | Certified Ethical Hacker — globally recognised certification for ethical hackers |
| CERT-In | Computer Emergency Response Team India — government body that handles cybersecurity incidents in India; under MeitY |
| Bug Bounty | Programs where organisations reward individuals for responsibly discovering and reporting security vulnerabilities |
| Penetration Testing (Pen Test) | Authorised simulated cyber attack on a system to evaluate its security |
| Software Piracy | Illegal copying, distribution, or use of copyrighted software without authorisation |
| Honeypot | A decoy computer system set up to detect, deflect, or study hacking attempts |
| Dark Web | Part of the internet not indexed by search engines; accessible only via special browsers (Tor); used for illegal activities |
| Phishing Kit | A ready-made package of tools used to create convincing phishing websites |
| Shoulder Surfing | Physically looking over someone's shoulder to capture passwords or PINs |
| Dumpster Diving | Searching through trash to find discarded documents containing sensitive information |
Cyber Laws in India
| Law | Year | Key Provisions |
|---|---|---|
| IT Act (Information Technology Act) | 2000 (amended 2008) | India's primary law governing cyberspace; covers cybercrime, digital signatures, electronic contracts, data protection; Section 66 (hacking), Section 67 (publishing obscene material), Section 43 (unauthorised access) |
| DPDP Act (Digital Personal Data Protection Act) | 2023 | India's first comprehensive data protection law; governs how personal digital data must be collected, stored, processed, and protected; establishes the Data Protection Board of India |
| IT (Amendment) Act | 2008 | Extended IT Act 2000; added provisions for cybercrime, data protection, Section 66A (later struck down by Supreme Court), new categories of cybercrime |
| IT Rules | 2021 | Regulates social media intermediaries (like Twitter, Facebook); requires grievance officers; traceability of messages; content removal timelines |
Key IT Act Sections:
| Section | Offence | Punishment |
|---|---|---|
| Section 43 | Unauthorised access to computer systems | Compensation up to ₹1 crore |
| Section 65 | Tampering with computer source code | Up to 3 years imprisonment + fine |
| Section 66 | Computer-related offences (hacking) | Up to 3 years imprisonment + ₹5 lakh fine |
| Section 66C | Identity theft | Up to 3 years + ₹1 lakh fine |
| Section 66D | Cheating by impersonation online | Up to 3 years + ₹1 lakh fine |
| Section 67 | Publishing obscene material online | Up to 5 years + ₹10 lakh fine |
| Section 70 | Unauthorised access to protected systems | Up to 10 years imprisonment |
Memory Tricks
🔑 First Virus and First PC Virus:
First virus: Creeper (1971) — "Creeper Came first in '71" First PC boot sector virus: Brain (1986) — "Brain was Boot sector in '86"
🔑 Virus vs Worm vs Trojan:
Virus = Virus Victs files (attaches + needs human action) Worm = Worm Wriggles through network (self-spreading, no host) Trojan = Trojan is Trickery (disguised, does NOT replicate)
🔑 Security Components — "CIA + NPA":
Confidentiality | Integrity | Availability (the CIA Triad — core of security) Plus: Non-repudiation | Privacy | Authentication
🔑 Types of Attacks — "HPSS DM":
Hacking | Phishing | Spoofing | Salami | DDoS | Man-in-the-Middle
🔑 Authentication Factors — "KHA":
Something you Know (password) Something you Have (OTP, token) Something you Are (biometric)
🔑 CAPTCHA Full Form:
Completely Automated Public Turing test to tell Computers and Humans Apart Remember: "CAPTCHA = Computer vs Human Automated Test"
🔑 WannaCry = 2017 = 150 countries = 200,000 computers:
"WannaCry made the world wanna cry in 2017"
🔑 IT Act 2000 + DPDP 2023:
IT Act 2000 = India's first cyber law DPDP 2023 = India's first data protection law "2000 for Cyber; 2023 for Data"
One-Liner Recap (Quick Revision)
- Cyber Security is the practice of protecting computer systems, networks, programs, and data from unauthorised access, damage, attack, or theft — a critical concern for the banking sector.
- The CIA Triad — Confidentiality (only authorised access), Integrity (data not altered without detection), and Availability (systems operational when needed) — forms the core of security.
- Cryptography is the science of secure communication — Encryption converts plain text to cipher text; Decryption reverses it; Symmetric encryption uses one key; Asymmetric uses a key pair.
- VIRUS stands for Vital Information Resources Under Siege — viruses are self-replicating malware that attach to host files and spread through human action (opening infected files).
- The world's first computer virus was Creeper (1971), and the first PC boot sector virus was Brain (1986) — created in Pakistan.
- A Worm self-replicates and spreads across networks automatically without human action and without needing a host file — unlike viruses that require human action to spread.
- A Trojan Horse appears to be legitimate useful software but contains malicious code — it does NOT self-replicate and must be installed by the user.
- Ransomware encrypts the victim's files and demands ransom payment (usually cryptocurrency) for the decryption key — WannaCry (2017) infected 200,000+ computers in 150 countries.
- Phishing is a cyber attack that fraudulently obtains passwords and sensitive information by impersonating a trusted entity through fake emails or websites.
- A DDoS (Distributed Denial of Service) attack floods a server with millions of requests from many compromised computers simultaneously, making it unavailable to legitimate users.
- A Firewall filters incoming and outgoing network traffic based on security rules — it acts as a barrier between trusted internal networks and untrusted external networks.
- Multi-Factor Authentication (MFA) requires two or more different factors (something you know + something you have + something you are) to verify identity before granting access.
- A Digital Signature authenticates the sender, ensures message integrity, and provides non-repudiation — it is legally valid in India under the IT Act 2000.
- Zero Trust Security operates on the principle "Never trust, always verify" — no user or device is automatically trusted, even within the corporate network perimeter.
- The IT Act 2000 (amended 2008) is India's primary cyber law; the Digital Personal Data Protection (DPDP) Act 2023 is India's first comprehensive data protection law.
Preparing for competitive exams requires consistent revision. Platforms like JobsMe simplify preparation through:
- Daily Current Affairs
- Weekly Current Affairs
- Monthly Current Affairs
- Static GK for Competitive Exams
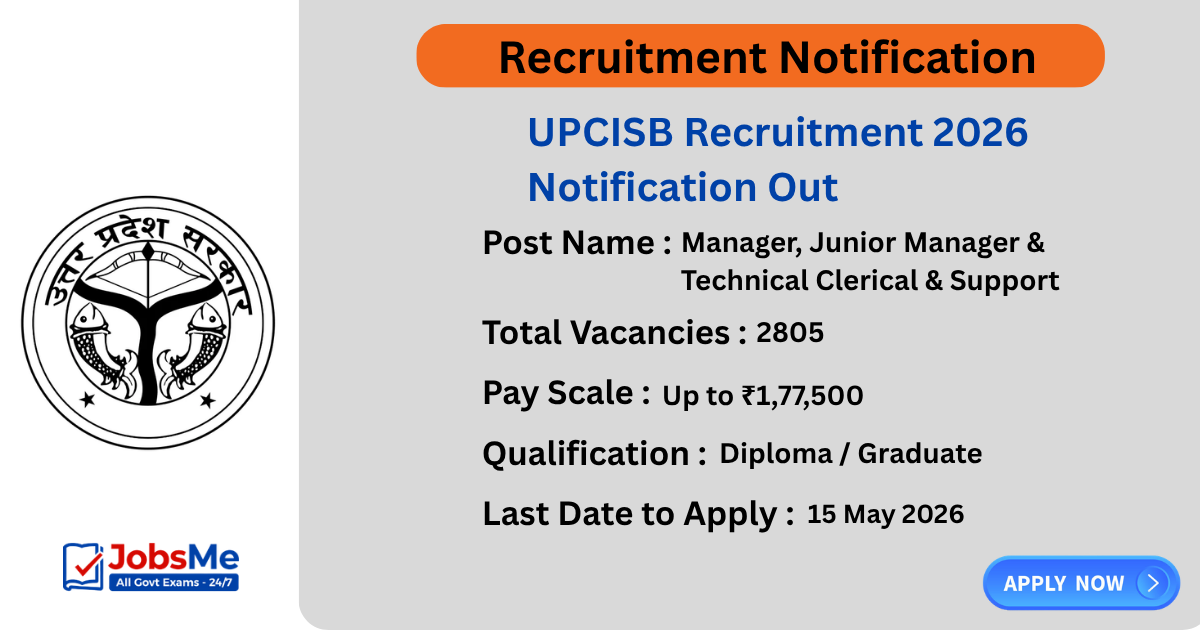
- Latest Government Jobs Notifications
- Banking Awareness
Stay updated, revise regularly, and attempt quizzes for better accuracy in UPSC, SSC CGL, IBPS PO/Clerk, SBI, RBI Grade B, RRB NTPC, Defence, and State PSC exams.
Free quiz • No signup required
Put this topic into practice with Current Affairs MCQ Quiz – 26 & 27 April 2026 | SSC Banking UPSC Railways Defence. It is the quickest way to reinforce what you just learned.
Frequently Asked Questions
What is the difference between a Virus, Worm, and Trojan Horse?
What is Ransomware and what was the WannaCry attack?
What is Phishing and what are its variants (Vishing, Smishing)?
What is the difference between DoS and DDoS attacks?
What is a Digital Signature and how is it different from a Digital Certificate?
What is the difference between Encryption and Decryption?
About the author